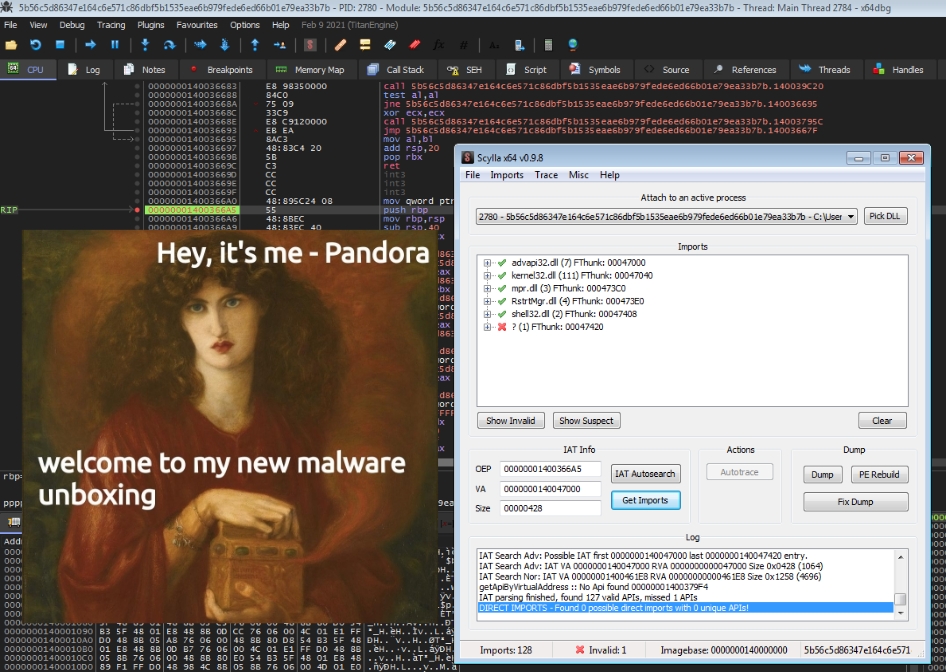
Quick revs: Pandora Ransomware - The Box has been open for a while...
Hey there, I’m finally getting around to introducing the new post category “Quick revs”, which will feature short write-ups of various malware …
Hey there, it has been a while, again.. 😅 This year was pretty stressful for me so far, so I didn’t really have the time to write about malware deep dives. This post is supposed to be an update about what I have been up to in the last couple of months and the changes I made to this site. Here is a short summary:
The dissectingmalwa.re blog was ported from the Pelican static site generator to Hugo. This enables me to include a few new features into the site and switch to a cleaner and prettier theme (+ a decent mobile layout). Don’t worry though, I purposely did not include any analytics or other tracking nonsense and as little javascript as possible into the new site. Unfortunately I cannot influence the tracking behaviour of embeds like Twitter posts or Youtube players, but these days a javascript blocker makes browsing the internet way better anyway.
Links to old blog aticles will stay active. I have started porting some of the old articles to the new site already, the rest will follow soon-ish…
Good news for the folks using RSS: Of course it did not kill this feature. The only thing that changed is the Feed URL, which you can also find in the footer of the page.
Since my last post in December 2020 about MountLocker ransomware I analysed lots of malware, but I simply haven’t had the time to write about it here. Instead I focused on the development of several tools, e.g. config extractors and unpacking tools for different malware strains which you can find down below or on my Github. I also made an upgrade hardware-wise and a few months back I got myself an IDA Pro license to step up my reversing game 💸
By far my most popular tool on Github right now: the setup script for my malware analysis environment. Contrary to FlareVM for example the script does not rely on the Chocolatey package manager so on the one side the tool list is easier to maintain yourself and the Installer won’t fail nearly as often, but on the other side the downloaded tools need to be installed manually (good if you want to customise stuff though 🤔). Eitherway MalwareLab_VM-Setup (the name does not flow nicely tbh) features a couple more tools and options (like avoiding tools with licensing that conflicts with commercial use, separate static and dynamic tool lists, preloading debugging symbols etc.). I try to update the tool lists every month to stay up to date. The readme also contains a few tips on setting up Windows 7 installs.
Back when REvil was still active I implemented this tool to extract the configuration from their Linux encryptors (pretty low effort since the config is stored in plain text).
Configzone is a config extractor for Warzone RAT and was inspired by the OALabs video series on Warzone. As far as I know it is the most complete open source extractor available right now. It is still missing a few value definitions though, so if you would like to contribute just send over a pull request :)
I’m also pretty proud that configzone is actually used in the field, thanks again for the shoutout reecDeep :D

Configmatter-windows is the most elaborate config extractor I have worked on this year. It supports Version 1 through 3 of the Windows variant of BlackMatter Ransomware. Implementing this tool has taught me a lot and IMO it is a pretty good target to practice config extraction on.
One of my recent weekend projects was a config extractor for the main component of Danabot. The implementation is not that robust yet and I’m going to make a few adjustments to it but if you would like to try it out, give it a go:
My latest config extractor as of now: for the Hancitor Loader. It is known to spread CobaltStrike Beacons and various Stealers for multiple years now and the activity does not seem to decrease. The implementation of the extractor is very simple, but the json output will be very useful for a future project that I cannot disclose yet :)
The following tools deal with open source packers/crypters that will IMO be used by crimeware (or worse who knows) sooner rather than later, so exploring detection possibilities and counter-measures makes sense. (Credit for the meme below: @Big_Bad_W0lf_)

With the Ezuri ELF crypter (developed by guitmz) the statement above about crimeware was already confirmed, since the TeamTNT group used it to obfuscate a Gafgyt DDOS malware sample (AT&T Report) in early 2021. The AES Key and IV are prepended to the encrypted payload embedded in the ELF and can be carved out. For more details see the repository below:
The Huan crypter is used for Portable Executable files and is ment to be used in Red Team engagements. The modus operandi of the unpacking tool is very similar to the Ezuri unpacker –> carving out the AES Key plus the encrypted payload and decrypting it.
Lastly there is zipExec which is another PE crypter of sorts but the loader is written in Javascript and the payload is stored in an encrypted zip archive.
Alright, that’s about it for the tools I have been working on this year. I have drafted two additional posts for this month where I want to introduce a new category/format for this blog, so stay tuned for that. Catch you later 👋
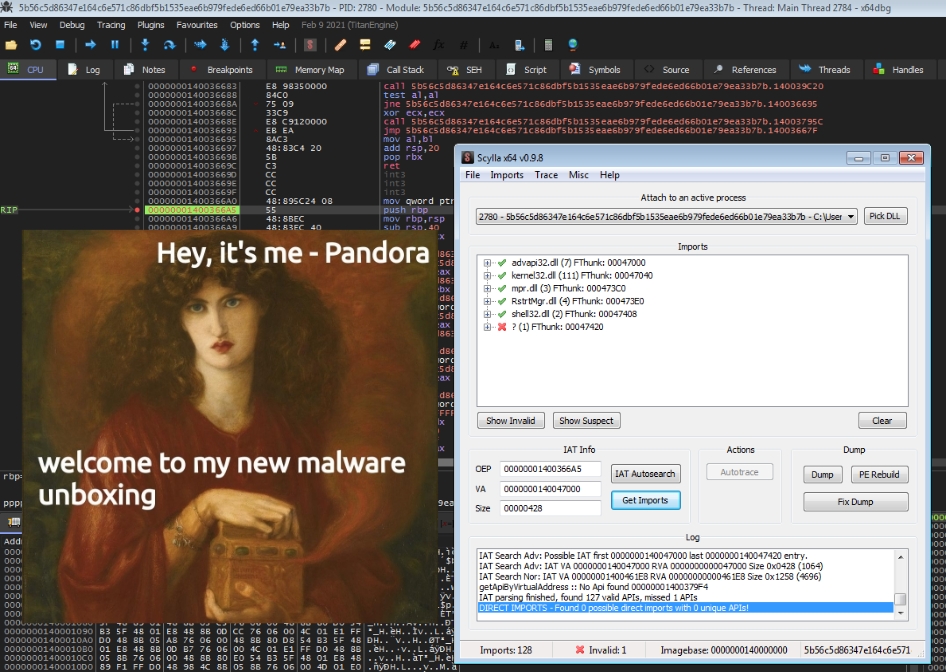
Hey there, I’m finally getting around to introducing the new post category “Quick revs”, which will feature short write-ups of various malware …

Hey there, long time no blog post :D It’s not like I haven’t been doing any research the last couple of months, but between the whole Covid-19 …