Quick revs: Pandora Ransomware - The Box has been open for a while...
Hey there, I’m finally getting around to introducing the new post category “Quick revs”, which will feature short write-ups of various malware …

Honestly I couldn’t decide between the title above and “All crimes are paid“, but Sex Pistols fans will get it regardless ¯\(ツ)/¯
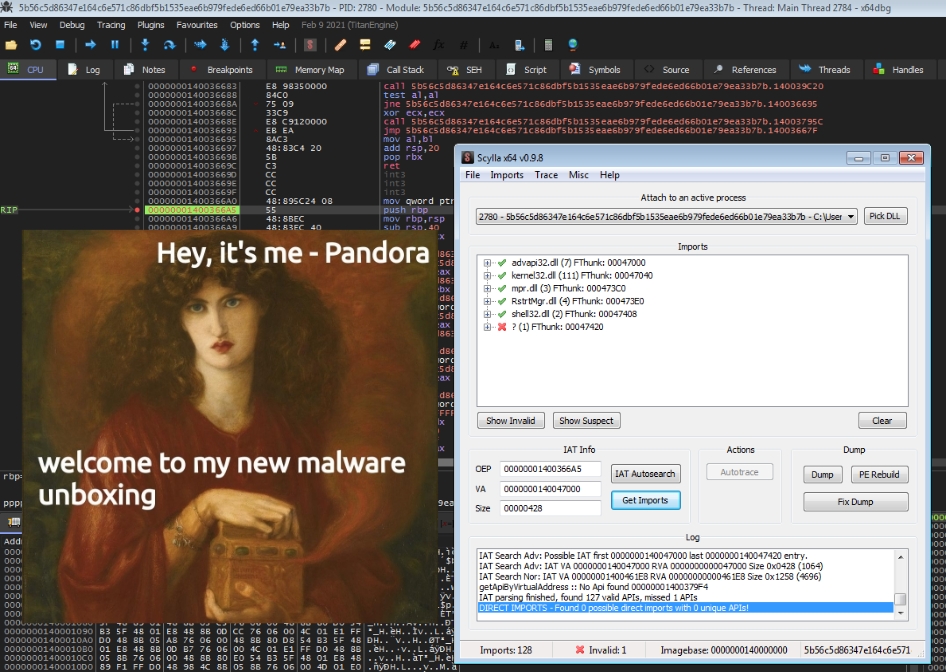
I found this sample while browsing the new public submissions on AnyRun on the 1st of December. It peaked my interest because there were just three samples of it on the platform at the time of writing this and they were all uploaded very recently.
SaveTheQueen @ AnyRun | VirusTotal | HybridAnalysis
–> sha256 3c9f777654a45eb6219f12c2ad10082043814389a4504c27e5aec752a8ee4ded
As always one of my go to tools is DetectItEasy. In this case it tells us that we are dealing with a .NET Application and you know what that means: Let’s whip out the .NET Analysis VM and take a look.
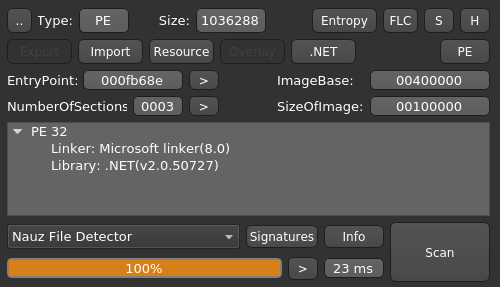
This looks pretty promising. Because .NET Code is not compiled to Machine Language directly but rather to the Common Intermediate Language (CIL) just in time we can inspect it without the need for a disassembler with Telerik JustDecompile or dnSpy.
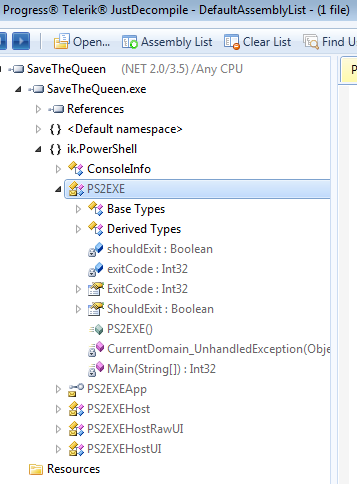
Looking at the Output it looks like we have a Powershell Script in front of us that has been run through PS2EXE, a kind of “converter” (a wrapper to be more precise) for ps1 scripts to PE executables.
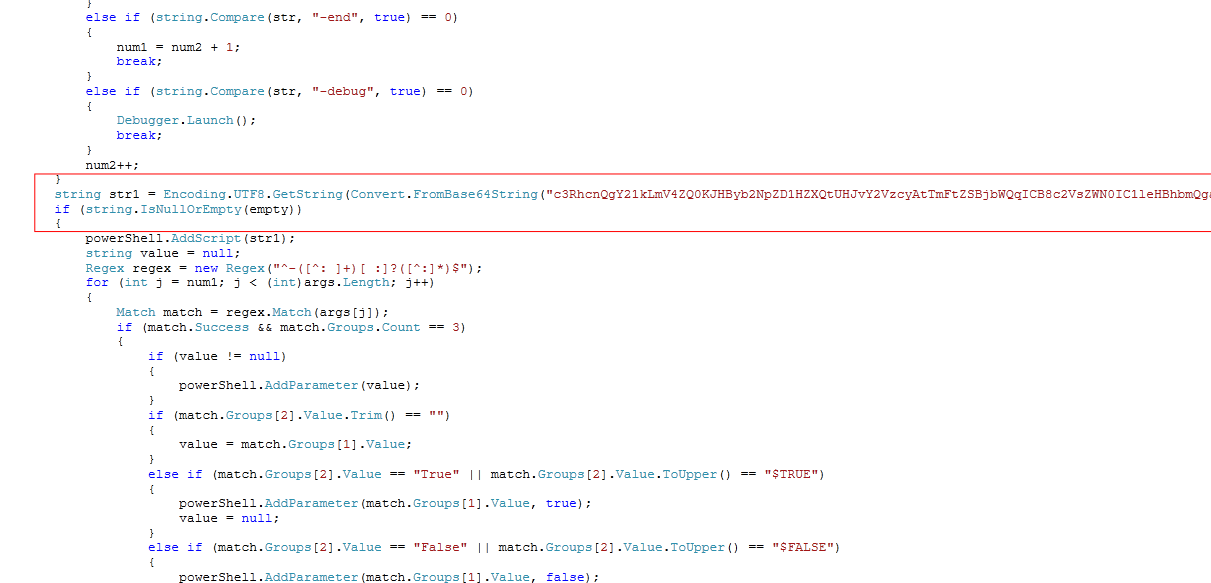
Decoding the Base64 string we got from the binary gets us two more blocks of what looks like base64 strings and a few lines of PowerShell code between it.
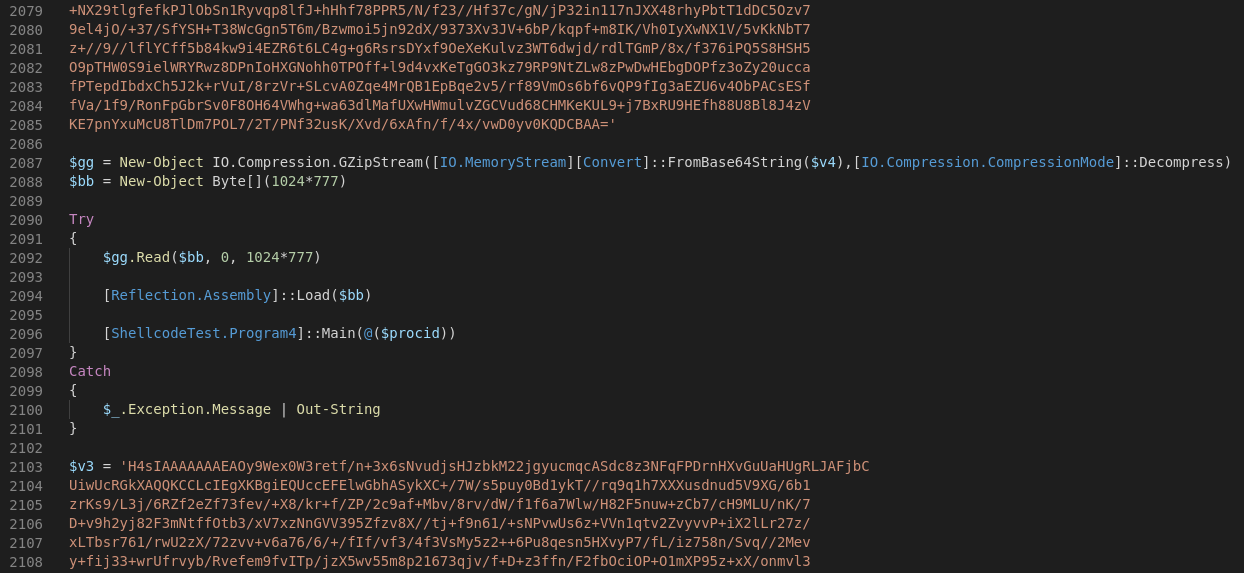
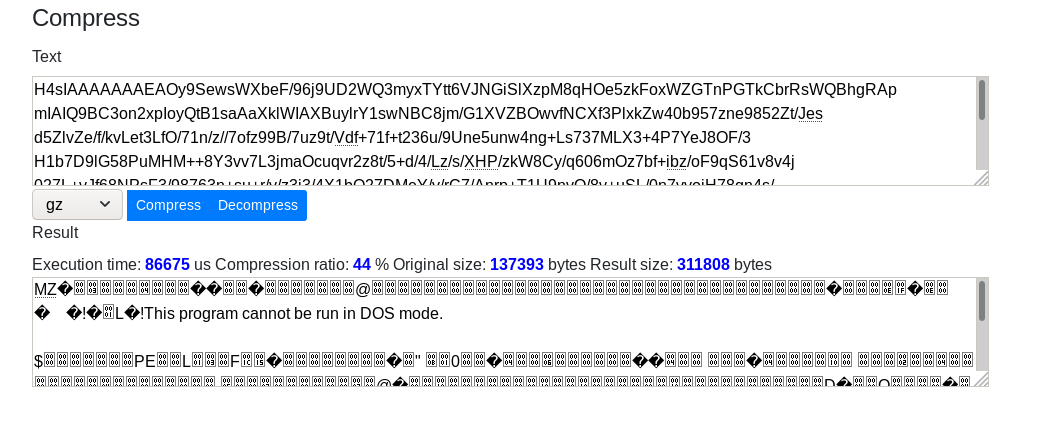
Decompressing one of the gzip blocks yields us a Portable Executable!
The dropped .SaveTheQueen.LOG was found in C:\ProgramData\. SaveTheQueen does not leave a ransomnote or other information to contact the crooks.
CLR: 2.0.50727.5420
Drive: C:\
Because the Registry edits resemble something seen before in LockerGoga I’d like to make a short comparison between the two stains.
| “Feature” | SaveTheQueen | LockerGoga | ||
|---|---|---|---|---|
| Ransomnote | none | txt File in %Desktop% | ||
| Logging | C:\ProgramData\SaveTheQueen.LOG | C:\.log | ||
| Registry | Restartmanager\Session00xx | Restartmanager\Session00xx | ||
| Binary | .NET | Visual C++ |
A new variant of the SaveTheQueen Ransomware was found the MalwareHunterTeam. I’ll update this article asap.
The SaveTheQueen ransomware is 😂...
— MalwareHunterTeam (@malwrhunterteam) December 18, 2019
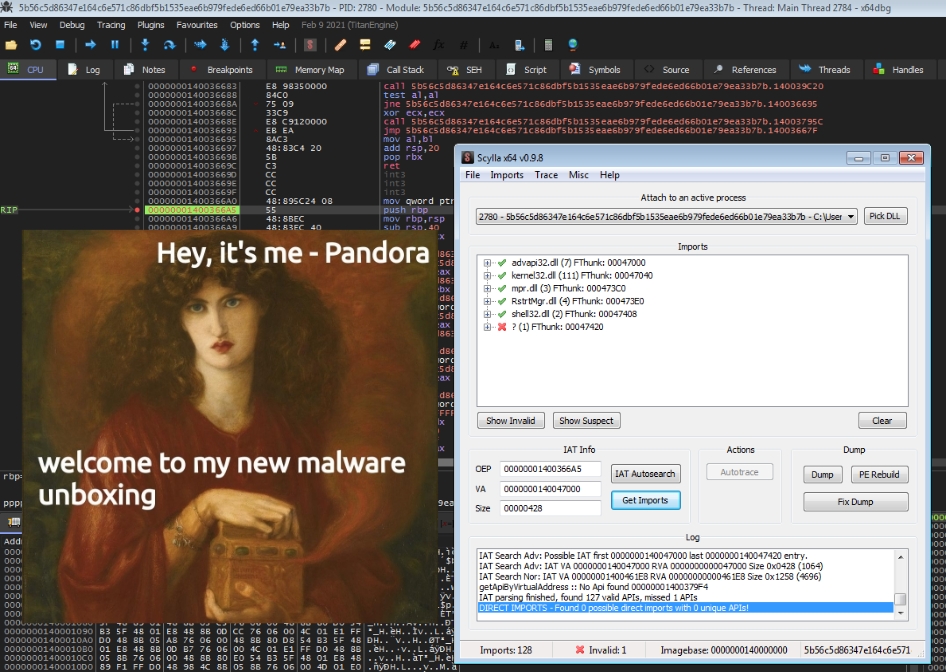
The ransomware sample -> ConfuserEx -> shellcode -> embed in C# injector dll (base64 encoded) -> PowerShell script (base64 + GZip) -> PS2EXE - and not even sure if that's all...@demonslay335
T1035 –> Service Execution –> Execution
T1215 –> Kernel Modules and Extensions –> Persistence
T1179 –> Hooking –> Persistence
T1055 –> Process Injection –> Privilege Escalation
T1179 –> Hooking –> Privilege Escalation
T1045 –> Software Packing –> Defense Evasion
T1055 –> Process Injection –> Defense Evasion
T1112 –> Modify Registry –> Defense Evasion
T1179 –> Hooking –> Credential Access
T1012 –> Query Registry –> Discovery
T1046 –> Network Service Scanning –> Discovery
T1120 –> Peripheral Device Discovery –> Discovery
T1057 –> Process Discovery –> Discovery
SaveTheQueen.exe --> SHA256: 3c9f777654a45eb6219f12c2ad10082043814389a4504c27e5aec752a8ee4ded
SSDEEP: 12288:a4Gvlgr3S/Jsftu5hU17WFKp4NpBvUssesKtIKy7vr4YT0PgZ304lGrDJo8YFfDY:ayw3ZwEaSAVX8Zye/
HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session00xx
Owner --> 6C 0A 00 00 26 23 E1 EB AC A6 D5 01
HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session00xx
SessionHash --> 32 Byte Hex
HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session00xx
RegFiles0000 --> Files to be encrypted/stolen
HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session00xx
RegFilesHash --> 32 Byte Hex
Hey there, I’m finally getting around to introducing the new post category “Quick revs”, which will feature short write-ups of various malware …
Hey there, it has been a while, again.. 😅 This year was pretty stressful for me so far, so I didn’t really have the time to write about malware deep …